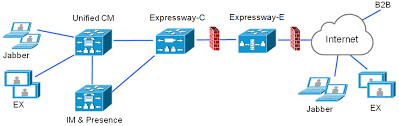
Cisco’s APIC-EM, or Application Policy Infrastructure Controller Enterprise Module is an OpenDayLight based SDN (Software Defined Network) controller. You could also possibly call it Cisco’s attempt to Merakify the Enterprise. On the bright side, it’s a free virtual appliance and no license is required.
One of the biggest features of APIC-EM is called Network Plug and Play
At a high level, the Cisco switch or router talks to the APIC-EM to streamline workflows and automate deployments. Switches and routers, known as agents discover the controller using any of the following mechanisms in order:
dhcp option 43 or dns (below), usb key, cloud discovery (currently beta), or the smartphone app.
DHCP
option 43 ascii "5A1N;B2;K4;I172.19.45.222;J80"
The option 43 string has the following components, delimited by semicolons:
- 5A1N;—Specifies the DHCP suboption for Plug and Play, active operation, version 1, no debug information. It is not necessary to change this part of the string.
- B2;—IP address type:
- B1 = hostname
- B2 = IPv4 (default)
- Ixxx.xxx.xxx.xxx ;—IP address or hostname of the APIC-EM controller (following a capital letter i). In this example, the IP address is 172.19.45.222.
- Jxxxx —Port number to use to connect to the APIC-EM controller. In this example, the port number is 80. The default is port 80 for HTTP and port 443 for HTTPS.
- K4;—Transport protocol to be used between the Cisco Plug and Play IOS Agent and the server:
- K4 = HTTP (default)
- K5 = HTTPS
DNS
APIC-EM: pnpserver.<customerdomain>.com NTP Server: pnpntpserver.<customerdomain>.com
The DHCP pool will need to either be on vlan 1, or you’ll need to specify a staging vlan on the upstream switch:
pnp startup-vlan 55
That brings me to another caveat of of Plug and Play is that the firmware needs to be supported, and may not match the shipping version of the hardware!
Another feature of APIC-EM is called Easy QoS
I actually really like this use-case for network programmability. It’s important for the policies to match end-to-end in QoS, so being able to roll out policies and get insights into your policy-maps holistically is kind of a big deal.
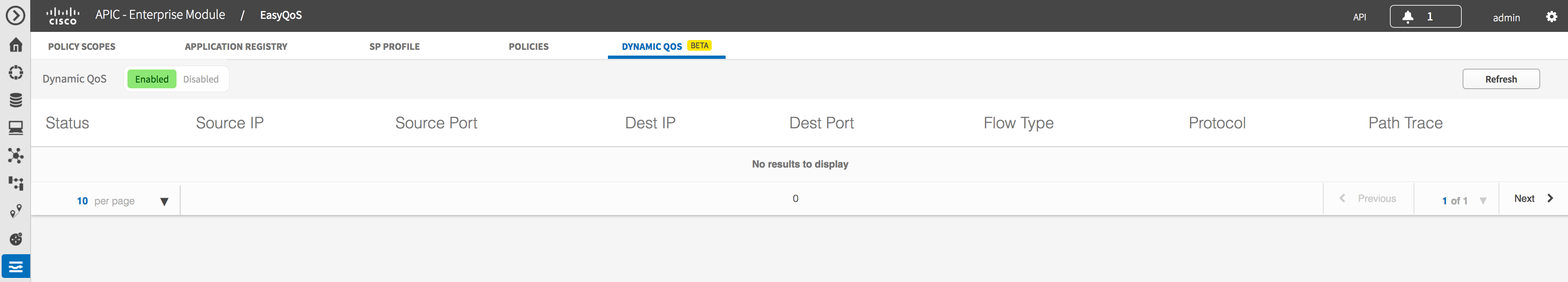
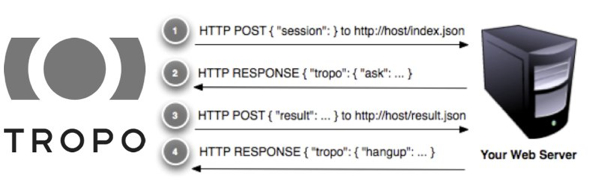
APIC-EM documentation gives the concept of Northbound, which is the REST API you can use for custom applications, and Southbound in which APIC-EM talks to hardware using SNMP and CLI. Cisco states “future APIC-EM releases will leverage other southbound technology such as NetConf as they become available”.
I found some Postman collections from CiscoDevNet’s Github page here. Postman collections are a great way to learn by doing.